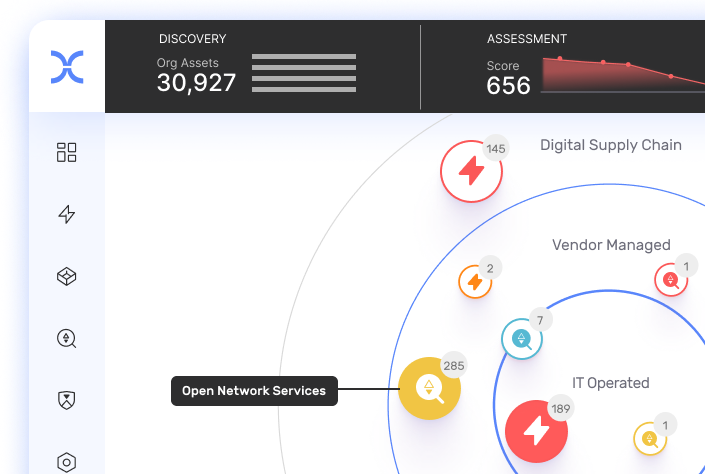
Discover your real attack surface
Gain complete visibility into all your organization’s exposed assets and risky connections – deep into the digital supply chain.
Learn More



Defend with the attackers’ perspective. Continuously identify, expose, and remediate critical threats faster.










Get broader coverage of your real attack surface including your digital supply chain, and sharper focus on your exploitable risks.
Gain complete visibility into all your organization’s exposed assets and risky connections – deep into the digital supply chain.
Learn MoreDynamically monitor risks across your entire inventory of digital assets and connections.
Learn MoreAutomate exploit simulation with non-intrusive security testing that won’t disrupt operations.
Learn MoreFocus on what needs to be addressed today – based on blast radius, exploitability, and threat intelligence.
Learn MoreAccelerate risk resolution with clear action items and integrated workflows across teams. And, gain automatic risk mitigation with IONIX Active Protection.
Learn MoreIn a world where organizations cannot fix everything, IONIX Threat Exposure Radar exposes critical threats so your security teams can improve your security posture.

”After working with IONIX for over a year, we are confident that its Ecosystem Security platform gives us the critical visibility we need to solve the difficult challenge of managing the risks and vulnerabilities in our entire digital supply chain.”
René Rindermann CISO, E.ON
Learn More

”It’s rare to find a cybersecurity solution that delivers almost immediate time to value with no impact on technical staffing. But that’s exactly what IONIX delivered.”
John Remo SVP Global Cloud / Infrastructure & Cybersecurity at WMG
Learn More
””I favor IONIX over our previous solution because it offers significantly deeper visibility into findings and also covers a much larger portion of our network.””
IT Security Officer at a Retailer with 10,001+ Employees
Learn More

”IONIX provides us the strategic advantage of seeing our external attack surface, dynamically, in the same way attackers see it.”
Mike Manrod CISO, Grand Canyon Education
Learn More
”We ultimately chose IONIX because of its ability to go beyond vulnerability detection and into automatic active protection that mitigated the risk of hijacking any of the company’s domains”
CISO, Fortune 500
Learn More

Continuously identify, expose, and remediate critical threats faster – from the attackers' point of view.
Explore More
Gain visibility into your real attack surface to systematically control and reduce attack surface sprawl.
Explore More
Expose your subsidiaries' attack surface and digital supply chain risks – empowering local teams to improve their security posture.
Explore More
Expose risk across public cloud platforms – understand what matters – and accelerate remediation with focus.
Explore More